This page was exported from Offer Free Microsoft and Cisco Exam Dumps
[
http://www.hitachidumps.com
]
Export date: Thu Oct 2 18:03:03 2025 / +0000 GMT
[December-2021]PT0-002 Exam VCE and PDF Free Download in Braindump2go[Q132-Q152]
December/2021 Latest Braindump2go PT0-002 Exam Dumps with PDF and VCE Free Updated Today! Following are some new PT0-002 Real Exam Questions! QUESTION 132 A. chmod u+x script.sh Answer: A QUESTION 133 A. obtaining PII from the protected network. Answer: C QUESTION 134 A. Understanding the tactics of a security intrusion can help disrupt them. Answer: A QUESTION 135 A. Edit the discovered file with one line of code for remote callback. Answer: C QUESTION 136 A. Whether sensitive client data is publicly accessible Answer: B QUESTION 137 A. Metasploit Answer: A QUESTION 138 A. Unsupported operating systems Answer: A QUESTION 139 A. To remove hash-cracking registry entries Answer: B QUESTION 140 A. The HTTP port is not open on the firewall. Answer: A QUESTION 141 A. Uncover potential criminal activity based on the evidence gathered. Answer: C QUESTION 142 A. Web archive Answer: A QUESTION 143 A. Run another scanner to compare. Answer: B QUESTION 144 A. WPS Answer: A QUESTION 145 A. Delete the scheduled batch job. Answer: C QUESTION 146 A. Partially known environment testing Answer: C QUESTION 147 A. Line 01 Answer: A QUESTION 148 A. Cost of the assessment Answer: B QUESTION 149 A. Establish the format required by the client. Answer: A QUESTION 150 A. Wardriving Answer: C QUESTION 151 A. Nessus Answer: B QUESTION 152 A. Nmap Answer: B 1.2021 Latest Braindump2go PT0-002 Exam Dumps (PDF & VCE) Free Share: 2.2021 Latest Braindump2go PT0-002 PDF and PT0-002 VCE Dumps Free Share: 3.2021 Free Braindump2go PT0-002 Exam Questions Download: Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!
Which of the following commands will allow a penetration tester to permit a shell script to be executed by the file owner?
B. chmod u+e script.sh
C. chmod o+e script.sh
D. chmod o+x script.sh
Explanation:
https://newbedev.com/chmod-u-x-versus-chmod-x
A compliance-based penetration test is primarily concerned with:
B. bypassing protection on edge devices.
C. determining the efficacy of a specific set of security standards.
D. obtaining specific information from the protected network.
A penetration tester is explaining the MITRE ATT&CK framework to a company's chief legal counsel.
Which of the following would the tester MOST likely describe as a benefit of the framework?
B. Scripts that are part of the framework can be imported directly into SIEM tools.
C. The methodology can be used to estimate the cost of an incident better.
D. The framework is static and ensures stability of a security program over time.
Explanation:
https://attack.mitre.org/
A penetration tester discovered a vulnerability that provides the ability to upload to a path via discovery traversal. Some of the files that were discovered through this vulnerability are:
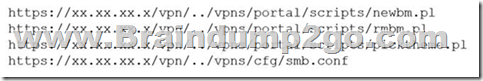
Which of the following is the BEST method to help an attacker gain internal access to the affected machine?
B. Download .pl files and look for usernames and passwords.
C. Edit the smb.conf file and upload it to the server.
D. Download the smb.conf file and look at configurations.
A company obtained permission for a vulnerability scan from its cloud service provider and now wants to test the security of its hosted data.
Which of the following should the tester verify FIRST to assess this risk?
B. Whether the connection between the cloud and the client is secure
C. Whether the client's employees are trained properly to use the platform
D. Whether the cloud applications were developed using a secure SDLC
A Chief Information Security Officer wants a penetration tester to evaluate the security awareness level of the company's employees.
Which of the following tools can help the tester achieve this goal?
B. Hydra
C. SET
D. WPScan
Which of the following is the MOST common vulnerability associated with IoT devices that are directly connected to the Internet?
B. Susceptibility to DDoS attacks
C. Inability to network
D. The existence of default passwords
Which of the following describes the reason why a penetration tester would run the command sdelete mimikatz. * on a Windows server that the tester compromised?
B. To remove the tester-created Mimikatz account
C. To remove tools from the server
D. To remove a reverse shell from the system
A penetration tester was brute forcing an internal web server and ran a command that produced the following output:
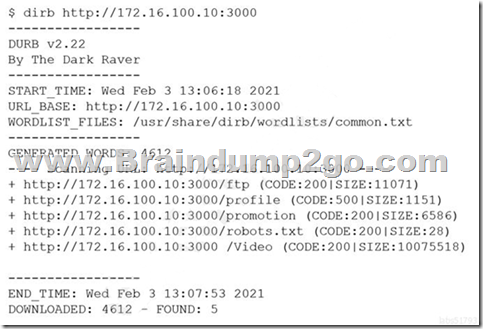
However, when the penetration tester tried to browse the URL http://172.16.100.10:3000/profile, a blank page was displayed.
Which of the following is the MOST likely reason for the lack of output?
B. The tester did not run sudo before the command.
C. The web server is using HTTPS instead of HTTP.
D. This URI returned a server error.
An Nmap scan shows open ports on web servers and databases. A penetration tester decides to run WPScan and SQLmap to identify vulnerabilities and additional information about those systems.
Which of the following is the penetration tester trying to accomplish?
B. Identify all the vulnerabilities in the environment.
C. Limit invasiveness based on scope.
D. Maintain confidentiality of the findings.
A company hired a penetration tester to do a social-engineering test against its employees. Although the tester did not find any employees' phone numbers on the company's website, the tester has learned the complete phone catalog was published there a few months ago.
In which of the following places should the penetration tester look FIRST for the employees' numbers?
B. GitHub
C. File metadata
D. Underground forums
A penetration tester completed a vulnerability scan against a web server and identified a single but severe vulnerability.
Which of the following is the BEST way to ensure this is a true positive?
B. Perform a manual test on the server.
C. Check the results on the scanner.
D. Look for the vulnerability online.
A company's Chief Executive Officer has created a secondary home office and is concerned that the WiFi service being used is vulnerable to an attack. A penetration tester is hired to test the security of the WiFi's router.
Which of the following is MOST vulnerable to a brute-force attack?
B. WPA2-EAP
C. WPA-TKIP
D. WPA2-PSK
Explanation:
https://us-cert.cisa.gov/ncas/alerts/TA12-006A
A penetration tester ran the following commands on a Windows server:
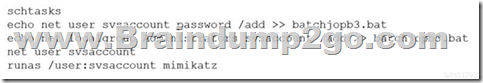
Which of the following should the tester do AFTER delivering the final report?
B. Close the reverse shell connection.
C. Downgrade the svsaccount permissions.
D. Remove the tester-created credentials.
A penetration tester is starting an assessment but only has publicly available information about the target company. The client is aware of this exercise and is preparing for the test.
Which of the following describes the scope of the assessment?
B. Known environment testing
C. Unknown environment testing
D. Physical environment testing
The following line-numbered Python code snippet is being used in reconnaissance:
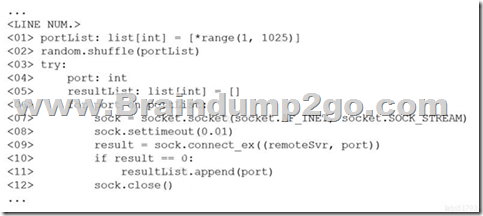
Which of the following line numbers from the script MOST likely contributed to the script triggering a “probable port scan” alert in the organization's IDS?
B. Line 02
C. Line 07
D. Line 08
E. Line 12
A consulting company is completing the ROE during scoping.
Which of the following should be included in the ROE?
B. Report distribution
C. Testing restrictions
D. Liability
A new client hired a penetration-testing company for a month-long contract for various security assessments against the client's new service. The client is expecting to make the new service publicly available shortly after the assessment is complete and is planning to fix any findings, except for critical issues, after the service is made public. The client wants a simple report structure and does not want to receive daily findings.
Which of the following is most important for the penetration tester to define FIRST?
B. Establish the threshold of risk to escalate to the client immediately.
C. Establish the method of potential false positives.
D. Establish the preferred day of the week for reporting.
A penetration tester has been hired to perform a physical penetration test to gain access to a secure room within a client's building. Exterior reconnaissance identifies two entrances, a WiFi guest network, and multiple security cameras connected to the Internet.
Which of the following tools or techniques would BEST support additional reconnaissance?
B. Shodan
C. Recon-ng
D. Aircrack-ng
A penetration tester conducts an Nmap scan against a target and receives the following results:

Which of the following should the tester use to redirect the scanning tools using TCP port 1080 on the target?
B. ProxyChains
C. OWASP ZAP
D. Empire
Explanation:
https://www.codeproject.com/Tips/634228/How-to-Use-Proxychains-Forwarding-Ports
A penetration tester received a .pcap file to look for credentials to use in an engagement.
Which of the following tools should the tester utilize to open and read the .pcap file?
B. Wireshark
C. Metasploit
D. Netcat
Resources From:
https://www.braindump2go.com/pt0-002-dumps.html
https://drive.google.com/drive/folders/1rj0Gt_C17MX5Yo1GbqsUWNNaSfwARr5I?usp=sharing
https://www.braindump2go.com/free-online-pdf/PT0-002-PDF-Dumps(Q132-Q152).pdf
Post date: 2021-12-29 02:46:03
Post date GMT: 2021-12-29 02:46:03
Post modified date: 2021-12-29 02:46:03
Post modified date GMT: 2021-12-29 02:46:03
Powered by [ Universal Post Manager ] plugin. MS Word saving format developed by gVectors Team www.gVectors.com